“The complexities of cloud computing, and the chance of human error will bite you, so don’t skimp on security planning before deployment or security validation after deployment.” — David Linthicum, InfoWorld
There is no denial in this fact that the cloud computing has transformed the very face of IT in the last few years. Consequently, it has changed the world of cybersecurity as well in the Cloud. Moreover, it has made the security vendors to rush for maintaining their product strategy. As they lacked scalability, compatibility and agility that are required for the cloud.
Indeed, it is a great feat for the cloud customers because now they are capable of keeping control over their implementing security. It is based on the shared responsibility model of cloud security to safeguard their platform, content, applications, networks and systems. The plus point is that they are no different than they would in an on-site data center.
Along with these leverages, the most attractive feature of this cloud computing is that the customers do not have risk visibility and control that were available in the data center previously.
What should the organizations do?
It is vital to define and implement a security governance plan for the cloud for all workload, micro services and containers of your organization. As you have moved to the cloud so it is high time to focus on Cloud security and compliance. It has become a business concern due to the constant growth of the regulations. However, in this regard, the organizations need to be cautious about having a comprehensive understanding of their regulatory compliance demands.
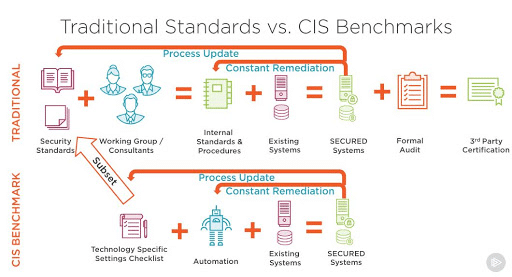
The maintenance of compliance across your public cloud computing is a key requirement for your business while your company is working in a high regulated industry. It is important to show shareholders, investors, workers and the public that your company abides by government regulations, existing laws and industry standards. So, compliance mandates for example CIS, PCI Compliance and HIPAA Compliance need businesses to track, protect and control access to sensitive data.
A view at some common Cloud Security challenges
In the first place, customers are able to understand that AWS is a platform that enables them to be compliant with regulations. But, be mindful that your cloud compliance is a shared responsibility. The real issue is the dynamic nature of the cloud that makes it very challenging. So, it is complicated to track and control activity with the constant modification of the workload configuration and updated applications.
The compliance requirements still exist due to unmodified cybersecurity. As a result of which audit tools and existing compliance often shortfall in the cloud. Practically the compliance means that the organizations are responsible for the security in the clouds. While the cloud service providers are responsible for the security of the clouds.
The right controls in place ensure that the systems are working according to the regulation. Plus, you will be capable of proving that these controls are operating. But, most of the time, the task of demonstrating CIS, PCI Compliance and HIPAA Compliance are complicated as compared to implementing the controls.
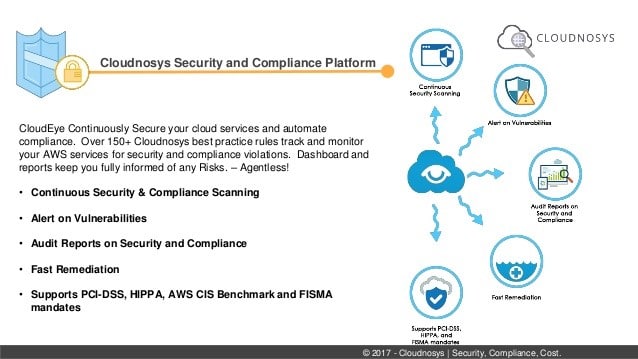
This is where the Cloudnosys works.
Cloudnosys – A comprehensive real time Cloud Security Threat Detection and Remediation Solution
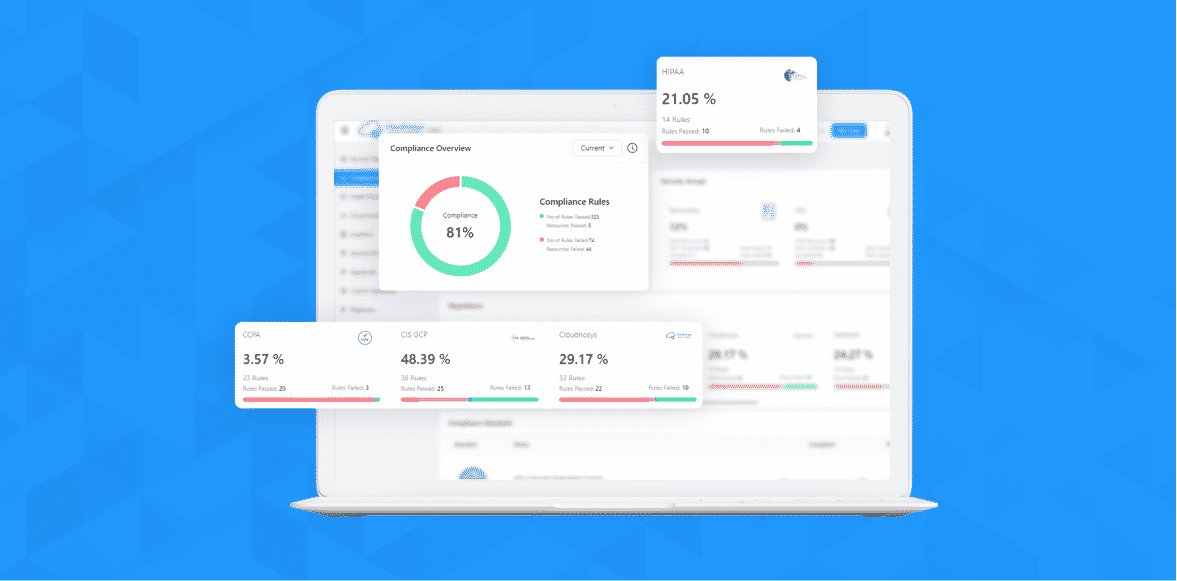
A number of organizations want true visibility into cloud computing environments. Here comes the Cloudnosys into play. This platform enables real threat defense across public cloud computing environments. For instance, Amazon Web Services. Below, you can see how we provide a unified view of CIS, PCI and HIPAA Compliance risks by associating different data sets of significant and distributed AWS environments.
What does Cloudnosys bring?
It is an uphill battle to map cloud resource configuration to compliance frameworks and keep an eye on them as they change and keep evaluating manually. This is not humanly possible as cloud velocity dicatates automation and born in the cloud native security solution. Therefore, Cloudnosys ease this by enabling you for monitoring, auto-remediating and reporting on CIS, PCI and HIPAA Compliance with our robust strategies.
Our areas of functionality are breaking into four parts. We deliver visibility and reporting that your business needs for its routine activities along with the reports for satisfying your auditors.
-
Mapping of resource configuration
Mapping your resource configuration and particular cloud usage to compliance controls across the numerous cloud services is the first step in assessing compliance. Cloudnosys has done the mapping of granular controls for usual compliance standards for instance, CIS, PCI and HIPAA Compliance. We provide over hundreds of out-of-the-box rules for Amazon Web Services.
-
Automatic profiling and resource discovery
As we have stated above that the dynamic nature of the cloud is the main reason why resources within the environment are at continuous change. Therefore, Cloudnosys discovers a resource just after its creation and outlines it to comprehend which policies to assess.
When the resource is discovered and identified as a database, it is permitted to assess for security controls such as encryption, and data access.
-
Fast remediation and continuous real-time monitoring
For evaluating the compliance posture of dynamic cloud environments, manual periodic audits are not effective. So, for violations, Cloudnosys constantly monitors computing resources of the cloud and automatically remediates problems. In this way, the encryption gets enabled automatically regardless of the database created with no encryption enabled.
-
An overview at our audit reporting
The companies are required to prove CIS, PCI and HIPAA Compliance for a specific time in an audit. It poses considerable variations in public cloud computing environments where customers make changes constantly with no security review. Cloudnosys enables you to report about your existing compliance posture. It also maintains previous snapshots of your cloud environment that assist you in proving compliance for every past period.
The CIS Compliance, PCI Compliance and HIPAA Compliance assurance report of Cloudnosys shows you,
- the executive summary of the results
- a comprehensive view of how many resources failed and how many passed the CIS, PCI and HIPAA Compliance checks
- the particular violated compliance controls and to get more information, you can click on any violation
- visibility into the resources that are scanned in the accounts for your specified regions
- Interactive dashboards
With our three interactive dashboards, you can view your cloud’s security posture.
- Security Dashboard
This dashboard provides a visualization for your cloud’s security aspects. It encompasses the details of each surface item that are found in your cloud with individual count. Moreover, security dashboard also details all resources and risks in a cloud service provider.
- Compliance Dashboard
Our Compliance Dashboard represents the brief detail of your cloud’s compliance environment. With this dashboard, you can view the details of total risks and number of scans that results in your all cloud accounts of Cloudnosys. Moreover, this dashboard displays individual risks and scan results of every compliance and cloud accounts regarding to security functions.
- Health Dashboard
It outlines your cloud environment health by charts about risks via security scans and groups. Get started with Cloudnosys
Cloudnosys allows threat defense across public cloud environments that includes AWS Web Services as well. We provide governance, visibility and compliance that provides a view of dangers across fragmented cloud environments.
You can get a free trial of Cloudnosys for 14 days. In this way, you will be well-versed about how it sets you free from all the issues that are related to compliance.