It is most certainly important to know your cloud environment when it comes to SaaS solutions. Most CIOs & security professionals are not fully aware of how many SaaS tools are used at their organization because it is so easy to sign up for them, and they are all leveraged via webhooks. They are not required to make firewall rule changes but, if your data is leaving your environment, that brings us to a few crucial questions. Do you know about all of your cloud environments? Do you understand what they are? Due to the number of vulnerabilities out there, there is a constant need to keep these things in check.
Apache Vulnerabilities
Apache is the world’s most widely used cross-platform web server software for Windows and LINUX/UNIX. Now, what makes Apache attractive to folks like, IT professionals, decision-makers, etc, is that it is open source. As vulnerabilities are exploited in the software, the open-source community tends to fix those problems proactively and share the source code with everyone. It makes Apache different from other proprietary software. On the other hand, it has been a victim of notorious vulnerabilities. Vulnerabilities can lead to data breaches. Some of the infamous Apache vulnerabilities are:
OpenMeetings SQL Injection Vulnerability
Version 1.0.0 of the Apache OpenMeetings was found vulnerable to SQL Injection Vulnerability. To exploit the vulnerability, the attacker will require being logged into the system. The immediate remediation is to upgrade to the latest version of Apache OpenMeetings.
Apache Ranger Security Bypass Vulnerability
Apache Ranger has been rendered prone to a security bypass vulnerability. If files outside these directories are not protected by the usual default configuration”require all denied”, these requests can succeed. If CGI scripts are also enabled for these aliased paths, this could allow for remote code execution. The immediate remediation is to upgrade to Apache Ranger’s latest version, which fixes this issue.
Path Traversal Attack Vulnerability
An attacker could use a path traversal attack to map URLs to files outside the directories configured by Alias-like directives. Certainly, this issue only affects Apache 2.4.49 and Apache 2.4.50 and not earlier versions. In Apache HTTP Server 2.4.51 this issue is fixed.
Apache HTTP Server Authentication Bypass Vulnerability
The Apache HTTP Server Vulnerability allows an attacker to bypass the authentication mechanism. The vulnerability stems from the improper use of the ap_get_basic_auth_pw() function of the Apache HTTP server by third-party modules. Safeguards include updating to the fixed version, network access to only trusted users, and employing IP-based access control lists (ACLs).
Mitigating Threats in the Cloud
Establish Foundational Elements
Establish your foundational elements early.
Name and Address
Check if you have named and addressed things correctly.
Security Policy
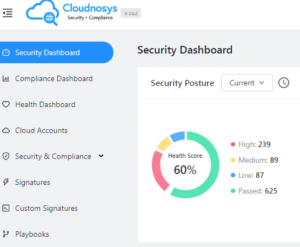
Check your security policy. Cloudnosys helps protect your cloud from data breaches and compliance risks.
Flow of Traffic
Check which traffic will flow where and if you have tagged it to understand what is going on in your environment,
Telemetry
You should have the right visibility to gather effective telemetry to know your environment. Check if you are collecting the right and effective signals, and they are useful to you from a telemetry perspective. Consequently, can you act on those signals once you have collected them or will they allow you to be able to respond in the event of a security issue?
Validation
To get others to validate what you assume to be true, get a third-party view, and validate what you think is a critical component of making sure your security program has integrity.
How Cloudnosys Can Help?
CloudEye
Our product CloudEye continuously secures your cloud services. It also automates your compliances and provides solutions for public clouds.
EagleEye
Our product EagleEye provides real-time threat detection and monitoring. It helps you protect your cloud infrastructure.
Organizations using Apache HTTP Server should monitor their system and review their patch level. Moreover, they should upgrade to the latest version available when required. Lastly, ensure that you have policy guardrails in place to meet security and compliance.