A #
Amazon Simple Storage Service (Amazon S3) #
Storage for the internet. You can use it to store and retrieve any amount of data at any time, from anywhere on the web
C #
Cloud Account #
A Cloud account is referred to as a single account in a cloud provider like AWS and AZURE. Cloudnosys platform serves like a bridge that uses the provided cloud account to run security checks, available for all enterprises who want Cloudnosys as a security shield for their cloud infrastructure.
A formal relationship with Cloudnosys that is associated with all of the following:
– The owner email address and password
– The control of resources created under its umbrella
– Payment for the activities related to those resources
The cloud account has permission to do anything and everything with all the account resources. This is in contrast to a user, which is an entity contained within the account.
Cloud Provider #
A company that provides cloud-based platform, infrastructure, application, or storage services to other organizations and/or individuals. Cloudnosys provides services to two major cloud providers; AWS and AZURE.
Cloud Resources #
These are essentially just resources on the cloud such as Servers, Disks, Databases, IPs, etc. deployed and running such as GCP Virtual Machines (VM), Azure, Storage, AWS EC2 Instance, Public IP, etc.
Cloud Tags #
See Tags below.
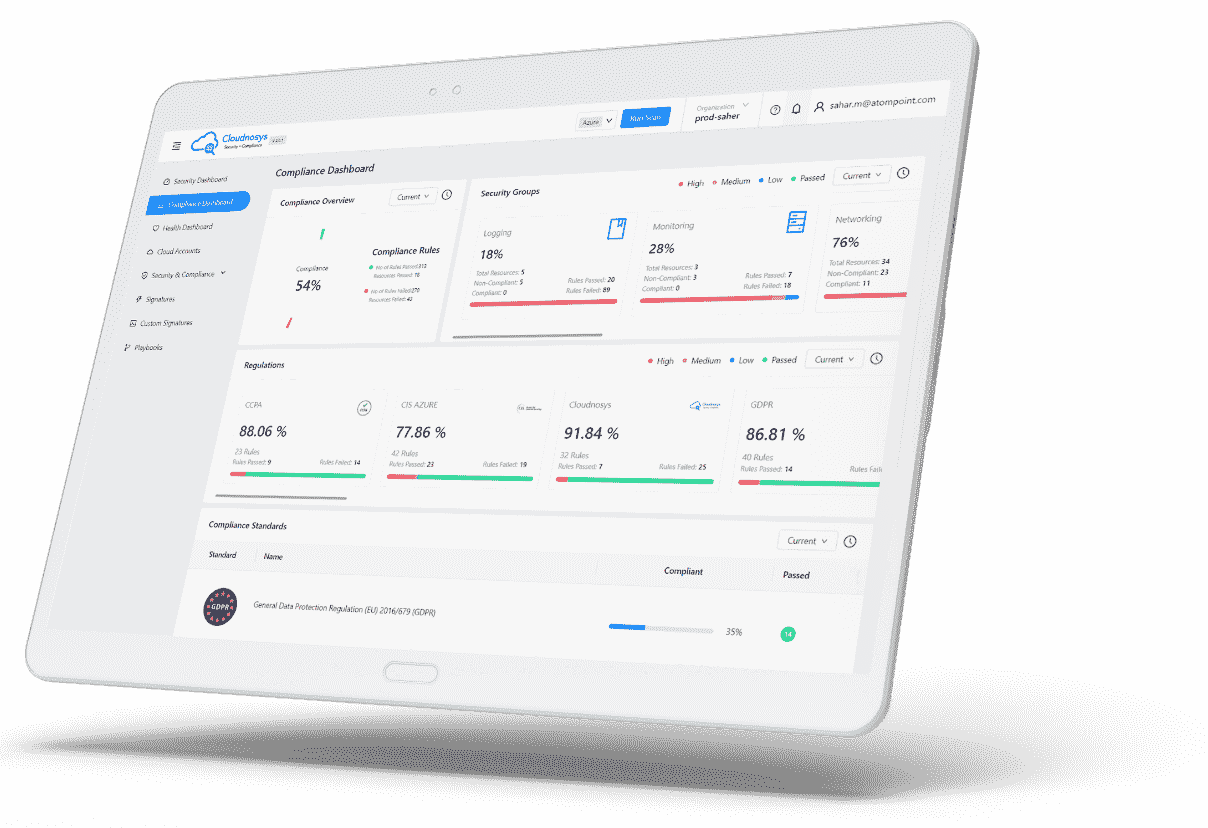
Compliance #
See Regulatory Compliance below.
Critical Risks #
Critical Risks depict the most severely affected security posture of resources.
Custom Signatures #
Check out this page instead: https://cloudnosys.com/docs/custom-signature/
G #
Governance #
Refers to the process of applying and managing certain principles or policies on cloud environments to ensure they maintain the requisite security standards. The main goal of cloud governance and compliance is to safeguard user interests and ensure cloud services are managed, distributed and delivered in the best way possible.
I #
Inventory #
It gives users a snapshot of their inventory on the cloud infrastructure (services distributed in categories: Computing, Storage, Network and IAM).
Playbooks #
Check out this page instead: https://cloudnosys.com/docs/introduction-to-playbooks/
R #
Regulatory Compliance #
In general, compliance means conforming to a rule, such as a specification, policy, standard, or law. Regulatory compliance describes the goal that organizations aspire to achieve in their efforts to ensure that they are aware of and take steps to comply with relevant laws, policies, and regulations.
Source: https://en.wikipedia.org/wiki/Regulatory_compliance
Remediate #
To remediate in Cloudnosys means to fix a risk or vulnerability.
Resource profile #
Resource profile portrays an outline of a specific resource such as resource health, failed and passed signatures
Risks #
A Risk is a threat or vulnerability that could negatively affect the confidentiality, privacy, reliability, and integrity of a provider’s services and can cause great damage to the user’s cloud environment.
A cloud infrastructure contains sensitive and critical data, such as personal, government, or business data. Hence, risks include unauthorized access to customer and business data, denial of service, insecure APIs, compliance violation, etc.
Role ARN #
Amazon Resource Name (ARN). A standardized way to refer to an AWS resource. For example: arn:aws:iam::123456789012:user/division_abc/subdivision_xyz/Bob.
Rule #
Rule is a set of conditions, you add rules and set conditions upon resources, whether you want to allow(pass) or block(fail) responses.
S #
Single Sign-On(SSO): #
A cloud-based service that simplifies managing SSO access to AWS accounts and business applications. You can control SSO access and user permissions across all your AWS accounts in AWS Organizations
Signatures #
In Cloudnosys, Signatures are essentially just security checks performed on Cloud Resources to check their violation for one specific issue.
Scan #
This is a detection process that runs security checks (or signatures) on all resources of the selected cloud account(s) as per certain criteria. Then the Scan Engine categorizes the signatures into Pass or Fail, etc.
Suppression #
When an alert is irrelevant, you can manually dismiss it. Cloudnosys provides a Suppression feature for this to automatically dismiss similar alerts in the future. Suppression can be used for:
- Suppress alerts that you’ve identified as false positives
- Suppress alerts that are being triggered too often to be useful
Security Groups #
A named set of allowed inbound network connections for an instance. (Security groups in Amazon VPC also include support for outbound connections.) Each security group consists of a list of protocols, ports, and IP address ranges. A security group can apply to multiple instances, and multiple groups can regulate a single instance in Cloudnosys you have groups like Performance,IAM,Networking & others.
T #
Tags #
Essentially people tag their cloud resources such as VMs or Storage to organize their infrastructure. They usually tag them by:
- Department or Business Unit, for e.g. department = ‘hr‘
- Project, for e.g. ‘cloudnosys‘ or ‘uber‘
- Any other personalized convention, such as “sensitive-data”
Also, tags are sometimes key-value pairs like project=fintech, or just singles ‘fintech‘.
U #
User #
A person or application under an organization that needs to make API calls to AWS products.
V #
VPC #
Virtual private cloud. An elastic network populated by infrastructure, platform, and application services that share common security and interconnection.
Virtual private cloud. An elastic network populated by infrastructure, platform, and application services that share common security and interconnection.